What's in the scan report
The full report contains several files. Here's an explanation of what's in each one and what it's for.
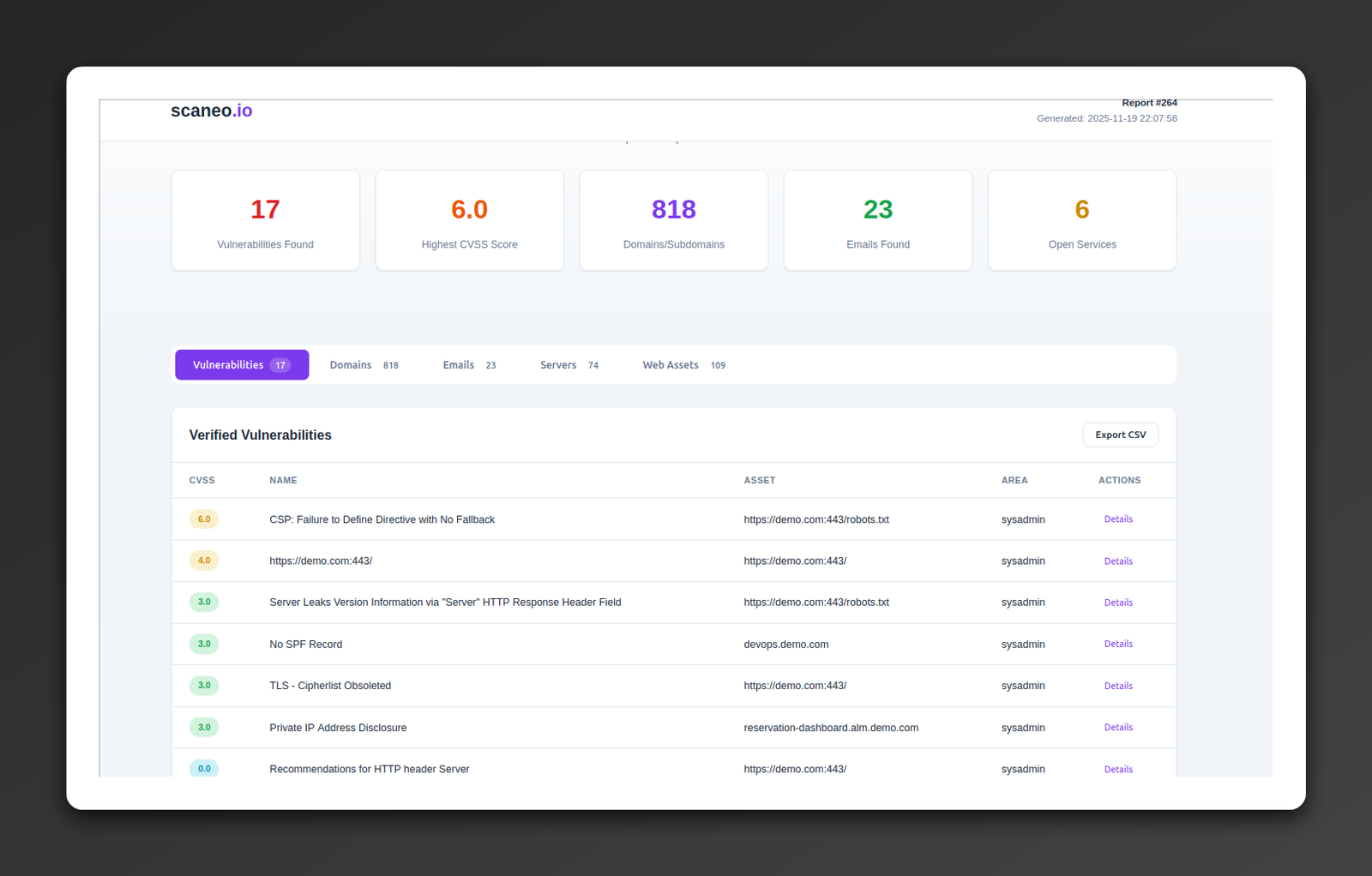
HTML report.html
What it is
Interactive browser-based version of all reports. Clear graphical display of data from the .csv files.
Why it's useful
Open the file in your browser. Easily filter results and navigate from overview charts directly to the details of individual issues.
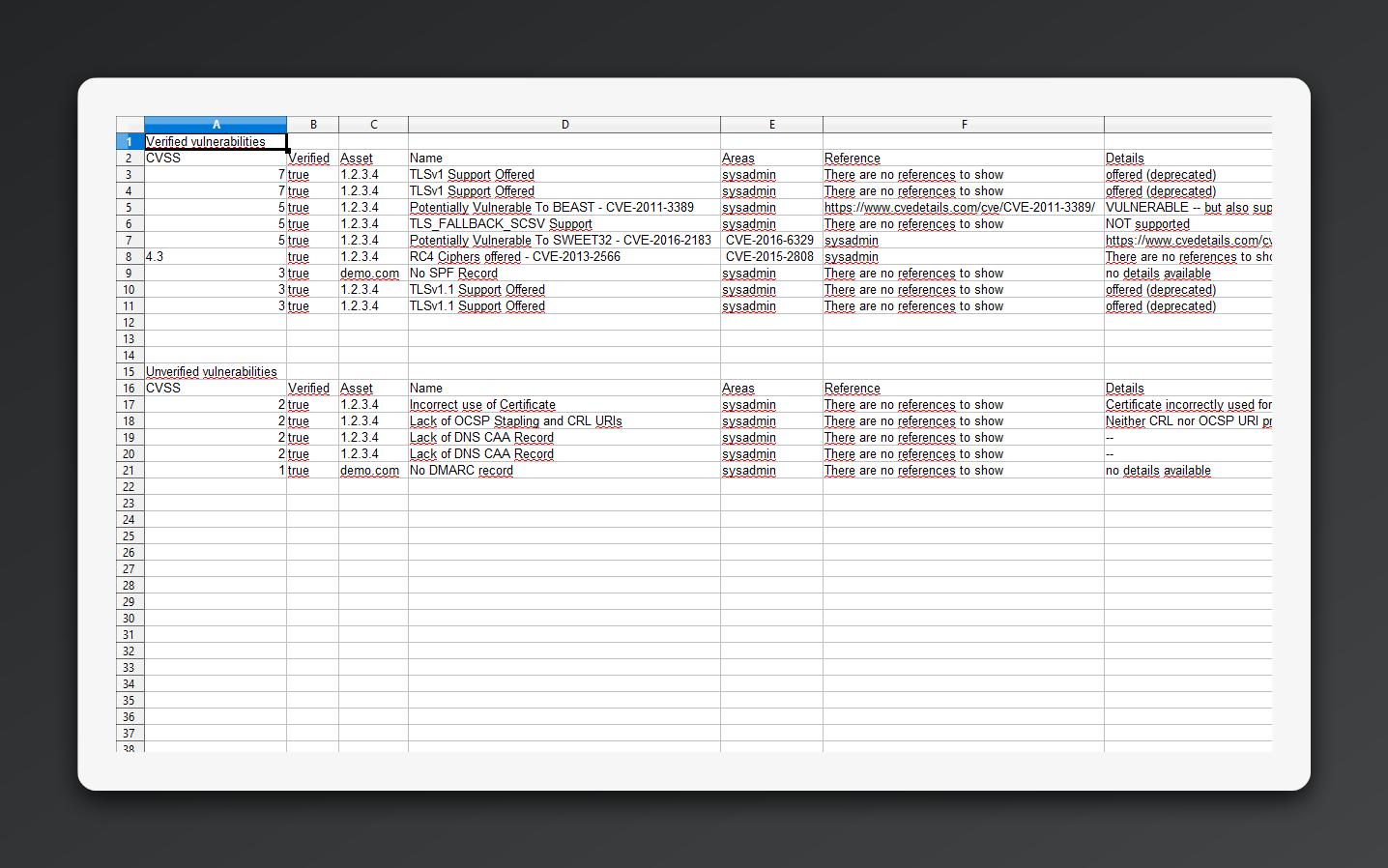
CSV vulnerabilities.csv
What it is
The most important file. A list of vulnerabilities supplemented with risk severity ratings.
How to read it
Each issue has a danger score (CVSS). The higher the number, the easier it is for a hacker to attack you. For each issue you'll find precise instructions for your IT person on what to do to patch the hole.
The list is divided into confirmed and unconfirmed vulnerabilities — suspicions that need to be verified on your side. Vulnerabilities are sorted by CVSS score. Each entry includes a link to the specific asset, description, location (backend, frontend, server), inputs/outputs, links to extended information, and scanner details.
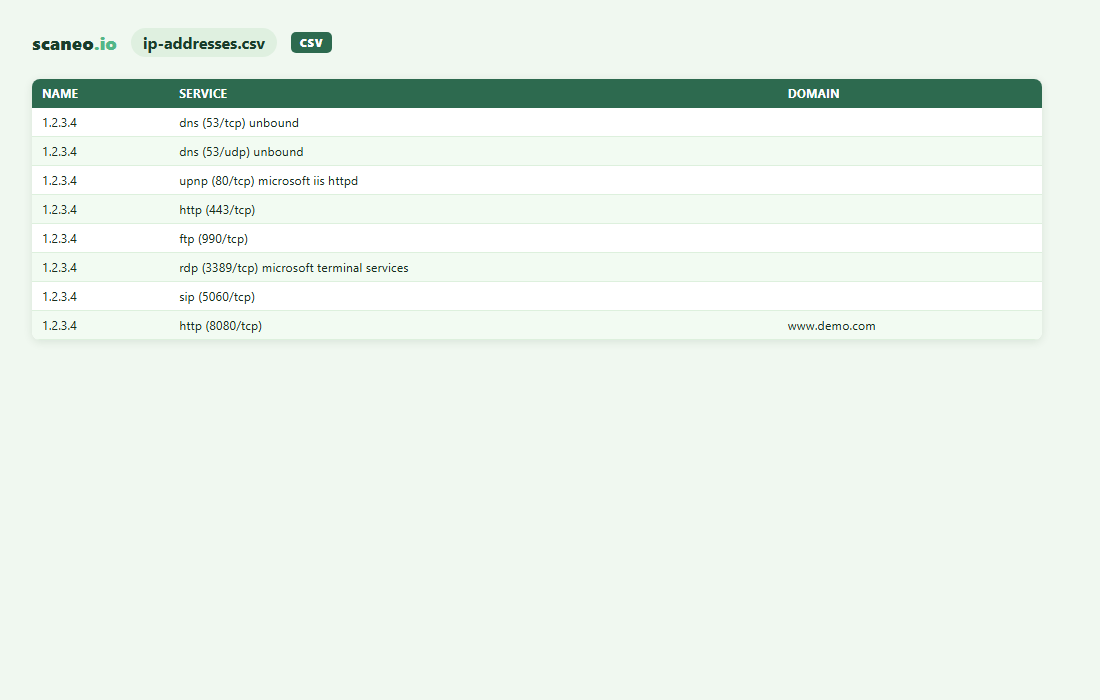
CSV ip-addresses.csv
What it is
A list of IP addresses and services accessible from the external network, including open TCP/UDP ports and specific software versions running on them.
Why it's useful
Unknowingly open ports ("addresses" of individual services on the server) are like a key under the doormat for a hacker.
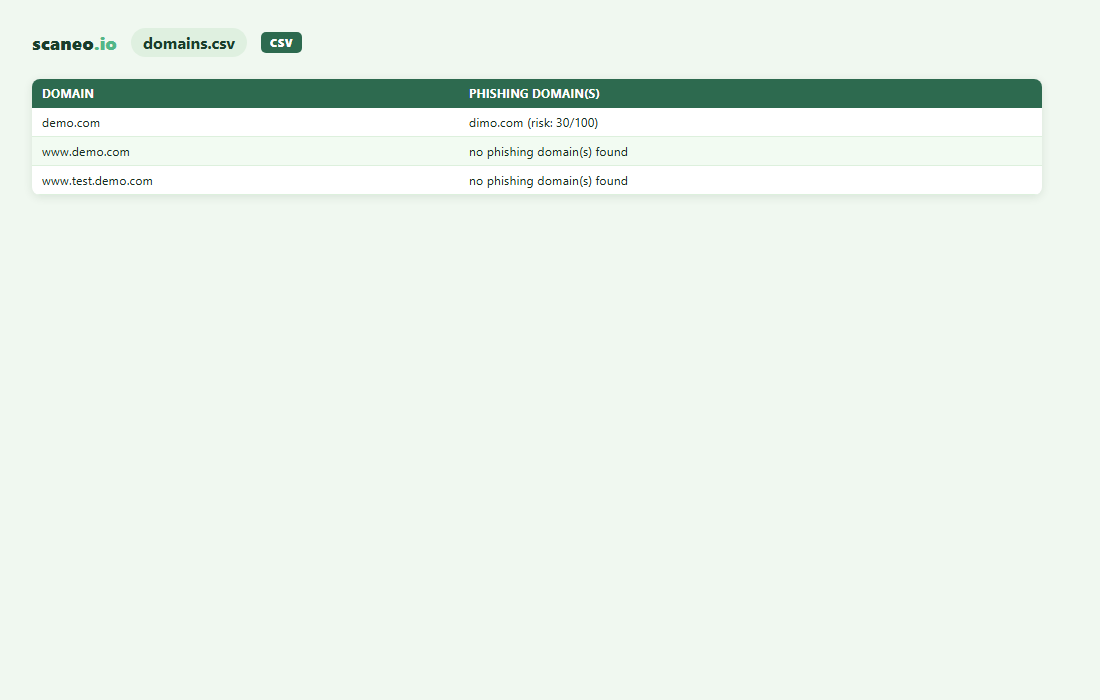
CSV domains.csv
What it is
A list of domains and subdomains associated with the main domain. Information on possible phishing domains and estimated attack risk.
Why it's useful
A phishing domain is a domain similar to yours that a hacker can use as a base for an attack (e.g. ldnes.cz vs idnes.cz — L instead of I).
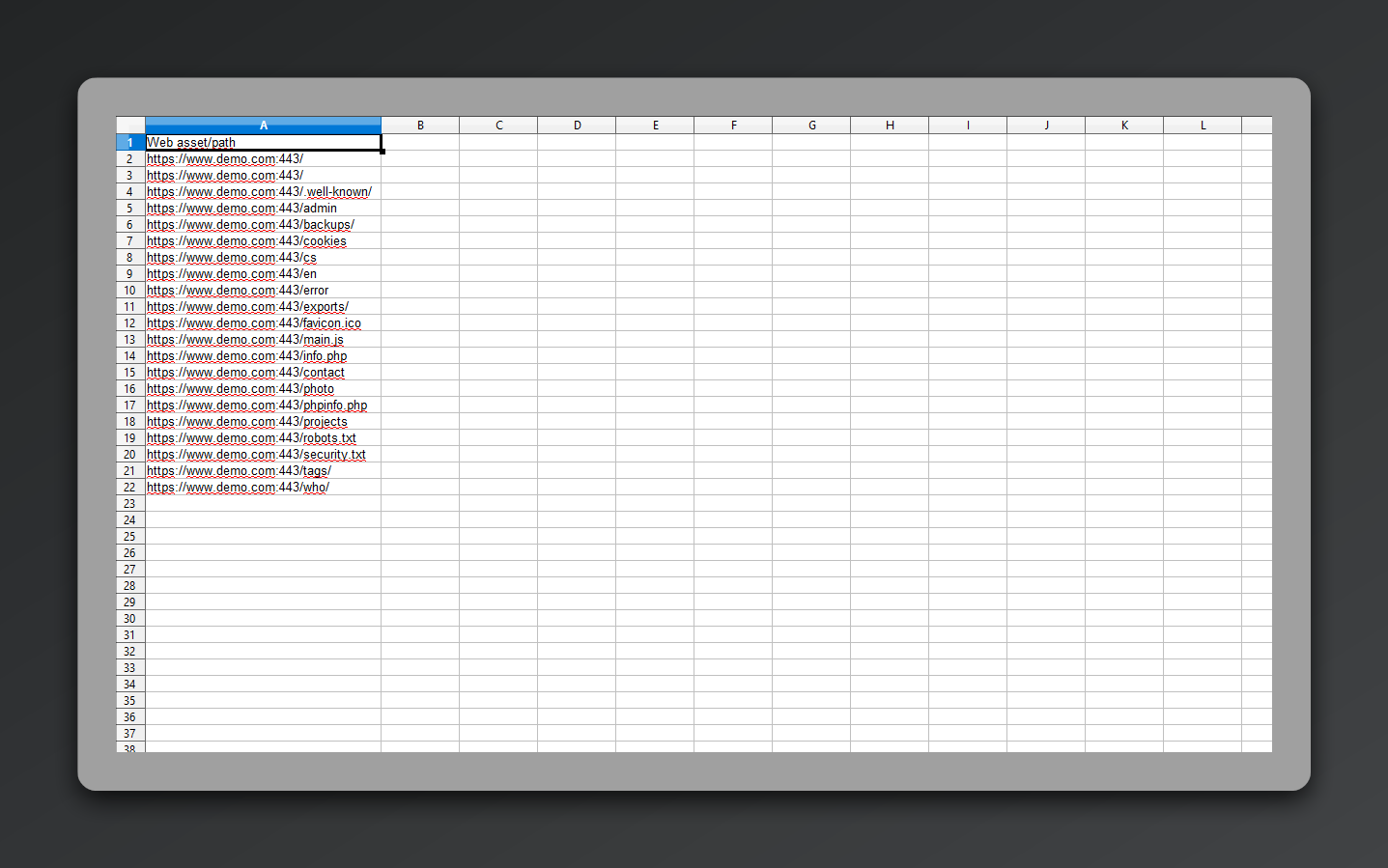
CSV webs.csv
What it is
A list of all URLs found by the scanner on your domain.
Why it's useful
These may be pages and directories with no inbound link that shouldn't be publicly accessible (backups, internal documents, etc.). Guessing their URL (e.g. yoursite.com/backups) is enough for a hacker to have them on a platter. Data that is only seemingly hidden needs to be found and locked down.
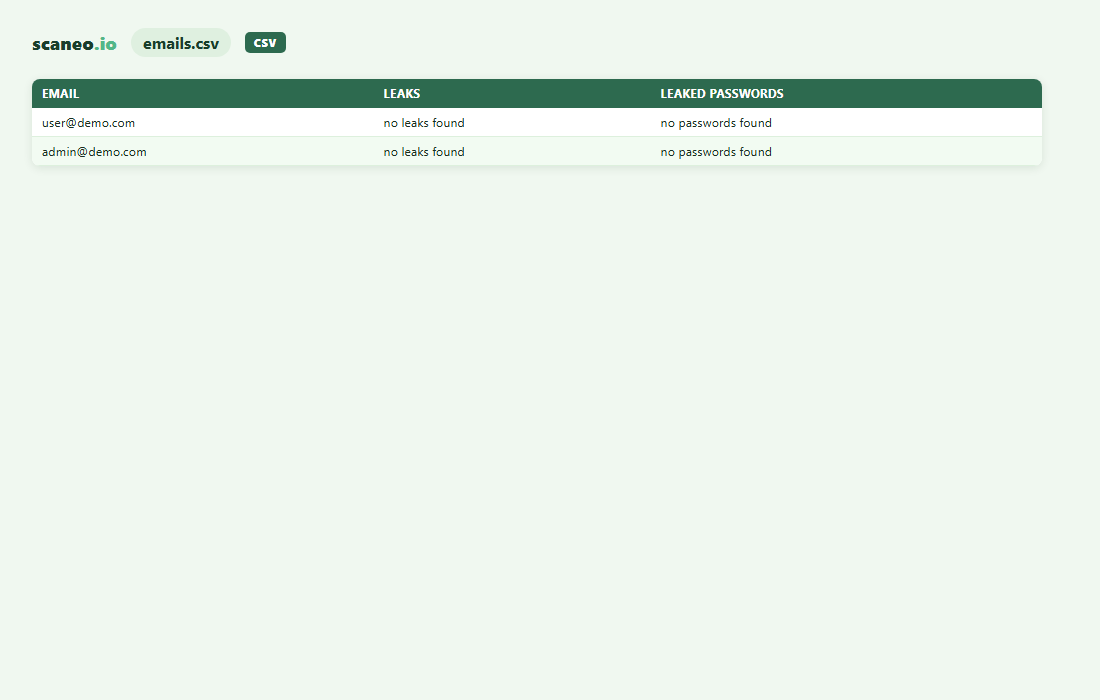
CSV emails.csv
What it is
A list of email addresses associated with the scanned domain.
Why it's useful
The scanner checks whether any of the addresses appear in a database of compromised emails.
Ready to see your own report?
Order a scan, get all these files delivered to your inbox within hours.
Order security scan